Importing or Creating Private Keys
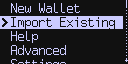
Import Existing#
If you already have a BIP-39 based wallet, or other private key material, you can import this directly into the Coldcard at setup time. Choose Import Existing from the main menu.
From the import menu, you can import seed words generated on another system, restore a backup file, import a raw XPRV or roll a dice to make your own value.
- 24 Words
- 18 words
- 12 Words
- Choose the number of words: 24, 18 or 12 words and the following menus will allow you to drill down to appropriate BIP-39 word (English only). The final word is a checksum value that verifies the other words. The Coldcard will calculate the 8 possible final words after 23 are provided.
- Restore Backup
- Import a backup file from another Coldcard. You will need the backup file (7z) on the MicroSD card, and you must enter a 12-word password that was provided at the time the backup was created.
- Clone Coldcard
- Starts the secure cloning process. You will need a MicroSD card. Insert it and a small file is written to it. While keeping the power active to this Coldcard, take that card to the source Coldcard from which you want to copy. Go to "Advanced > Backups > Clone Coldcard" and a special encrypted file is written to the card. Bring it back to the (still powered) blank Coldcard and press ✔. The data is restored and the Coldcard reboots. Everything except PIN code will be duplicated from the other Coldcard. Both Coldcards must be running v4.0.0 or higher firmware, and should probably be same version exactly.
- Import XPRV
- To import an XPRV, you must provide a cleartext file on MicroSD
with a BIP-32 base58-serialized extended master private key. It
should start with
xprvand be on a single line of a text file. The rest of the file is ignored. Please note there is no encryption for this method, and therefore, it is very hazardous and only recommended for testing purposes. - Dice Rolls
- You have the option of creating a unique seed value by rolling a six-sided dice (D6). Just keep pressing 1 - 6 as you roll. At least 99 rolls are required for 256-bit security, and if you operate with fewer rolls, you will be warned. Press ✔ when complete, and the equivalent seed words are shown so you can write those down instead of the dice numbers. As usual, the word quiz is conducted before the seed is saved. Learn how to completely verify the dice rolls using Tails
The final item in the menu is a bit different because it allows you to create the private key directly. In that way it's not really an 'key import', but a 'create key'.
Mix-in Dice Rolls#
This is not the only way to introduce entropy from dice rolls. Any time the Coldcard is showing the seed words on-screen, you may press 4 to "mix in" additional dice rolls. In this case, since the entropy of the Coldcard is being used as a starting point, it is safe to add as few or as many rolls as desired.
Import from TAPSIGNER to COLDCARD#
To import your Tapsigner backup (XPRV) to your Coldcard you must
have two things, the backup key located on the back of the card and
the .aes encryption file.
You can obtain the .aes file during the Tapsigner initial setup
(save it for later), or by having the Tapsigner card as well as the
correct pin.
Via CLI cktap proto:
type cktap backup which saves the card's XPRV into an AES-128-CTR
encrypted file with the current date.
To start, wipe any existing seed from your Coldcard so you have a
fresh device to import the TS backup to. Make sure an SD card is
inserted with the .aes file.
If you don't wish to store the XPRV and prefer a "one time use",
you can import it as a temporary seed — meaning you do not
need to Destroy Seed first. To do this, got to Advanced Tools
-> Temporary Seed -> Import Tapsigner Backup. This way the main
seed is preserved and Tapsigner Backup will only last until the
device is powered off.
From a fresh device, go to Import Existing -> Tapsigner Backup
and select the .aes file you loaded onto the SD card.
The Coldcard will then ask you to input the backup password which is located on the back of the Tapsigner.

Once entered, your Coldcard will generate the xprv and store it safely. You can now export the public key and view the funds on any Compatitble Software Wallet.
Extract TAPSIGNER XPRV (Raw)#
The TAPSIGNER can generate a backup file of its master private key. This file is protected by a factory-programmed password, which can be found on the back of the card.
To verify that your backup works correctly or to recover the private key, you can run the below command on the command line. Replace PASSWORD with your TAPSIGNER's backup password, and FILE with the path to your backup file.
openssl aes-128-ctr -iv 0 -K PASSWORD -in FILE.aes
If everything works correctly, you should be able to see the master private key printed out as simple text. The key starts with the prefix "xprv".
For best security, we recommend that you only run the above tools on a secure machine, and immediately remove the backup file afterwards.
WARNING: These steps will expose your private key to the local machine. Use at your own risk.
Nunchuk Recovery#
-
On the main screen under the keys subcategory, click the '+' button.
-
Select "Add NFC Key" then click "Recover From Backup".
-
Select the
.aesfile from your phone's internal storage or a cloud location. -
Input the backup code from the back of the Tapsigner.
-
Name your recovery key.
TAPSIGNER - Nunchuk Tutorial Video
Keep in mind that this is now a software key (hot) and no longer requires the Tapsigner to sign transactions.